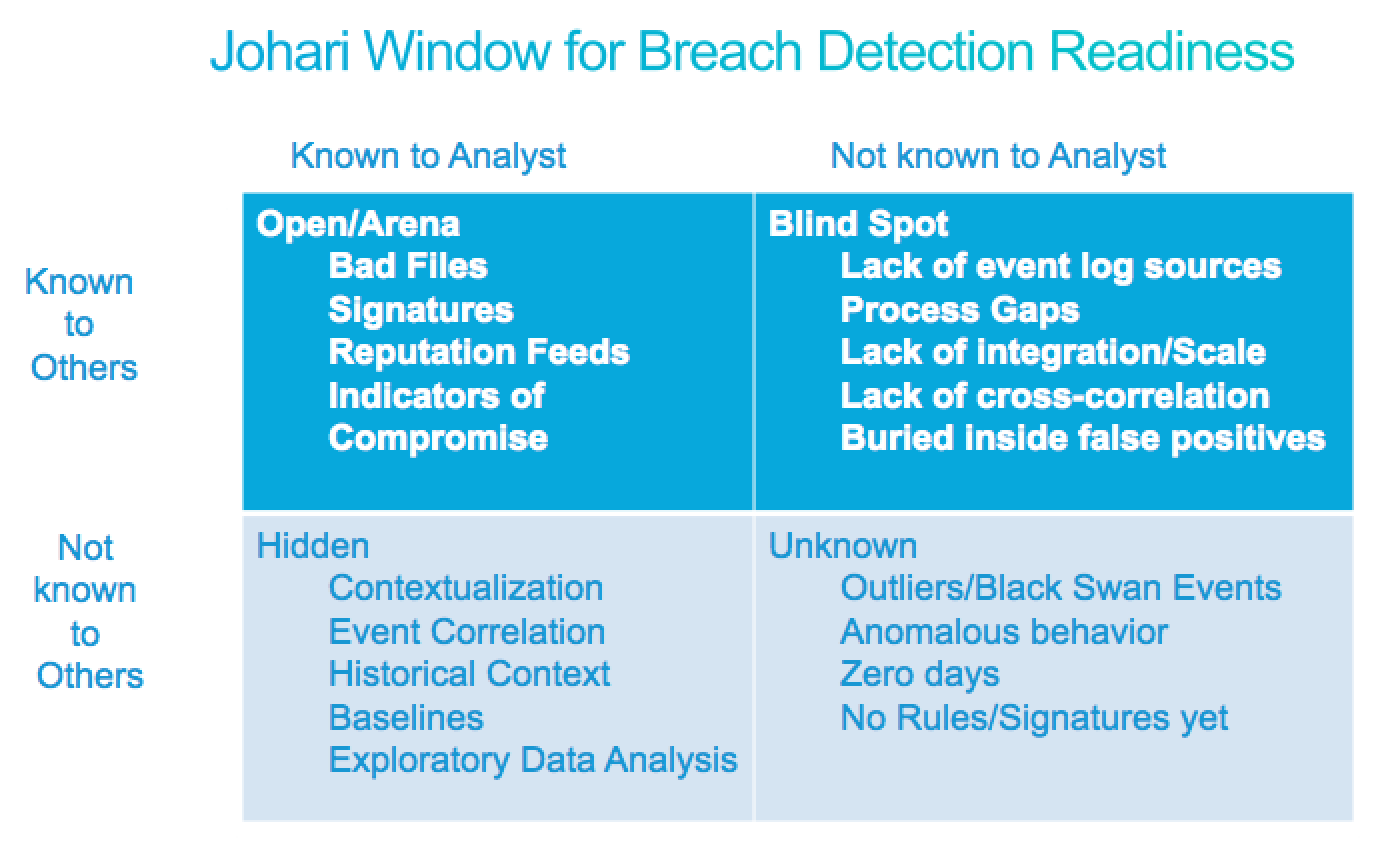
Revolutionizing SIEM Tools with Breach and Attack Simulation: Enhancing Detection and Response in IT Security - Get cyber-fit

Am I being breached? Data breach detection tools and tips to suit any organisation Am I being breached? Data breach detection tools and tips to suit any organisation

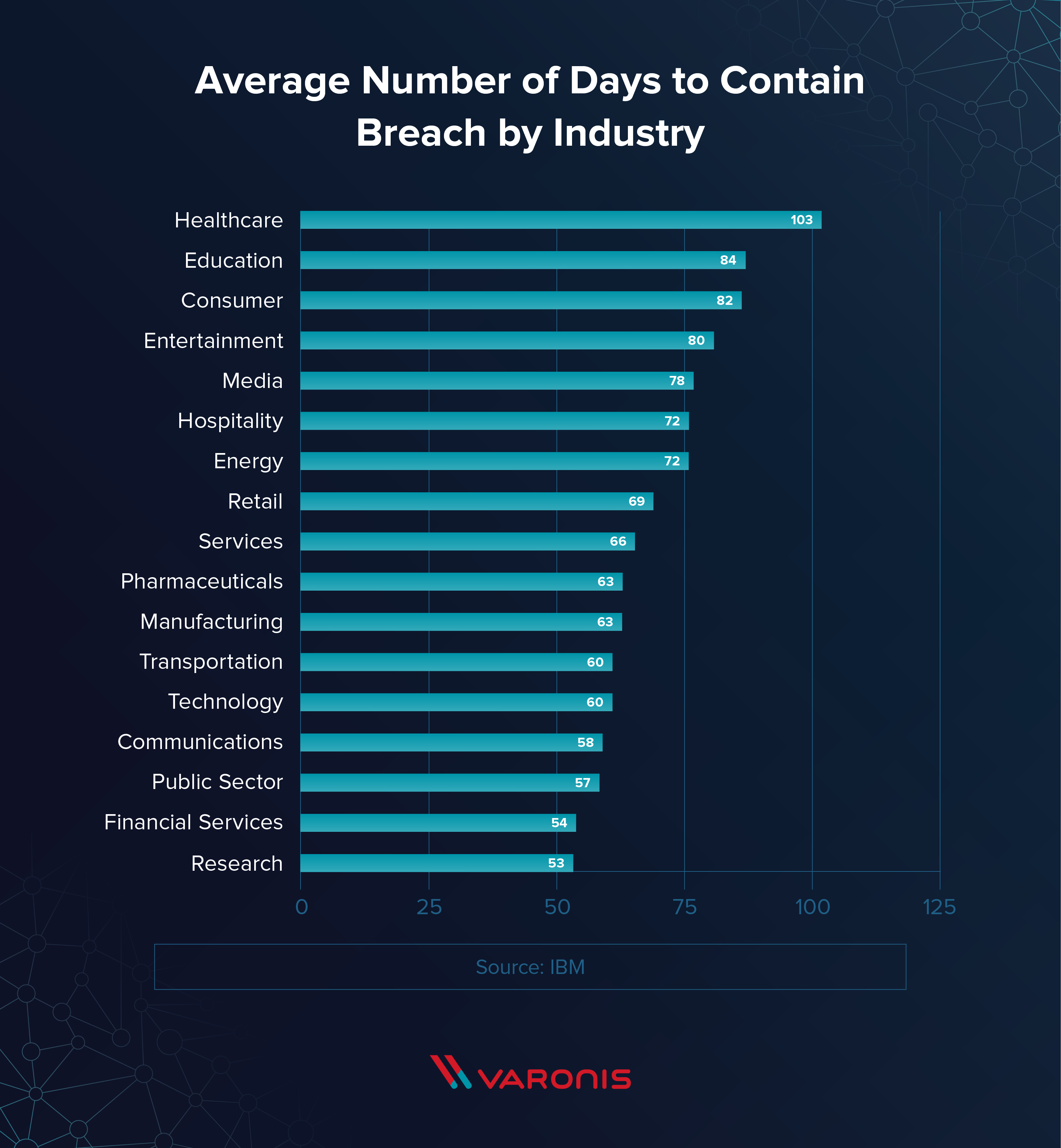
Enterprise data breach: causes, challenges, prevention, and future directions - Cheng - 2017 - WIREs Data Mining and Knowledge Discovery - Wiley Online Library

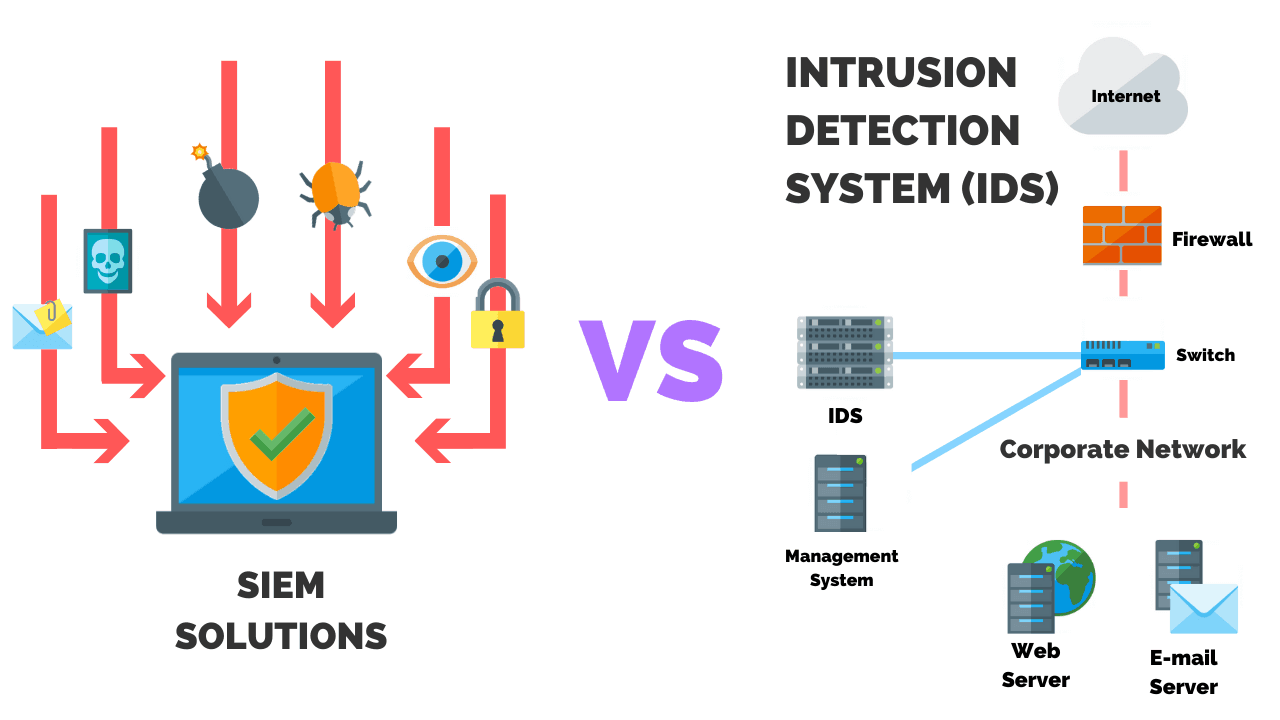
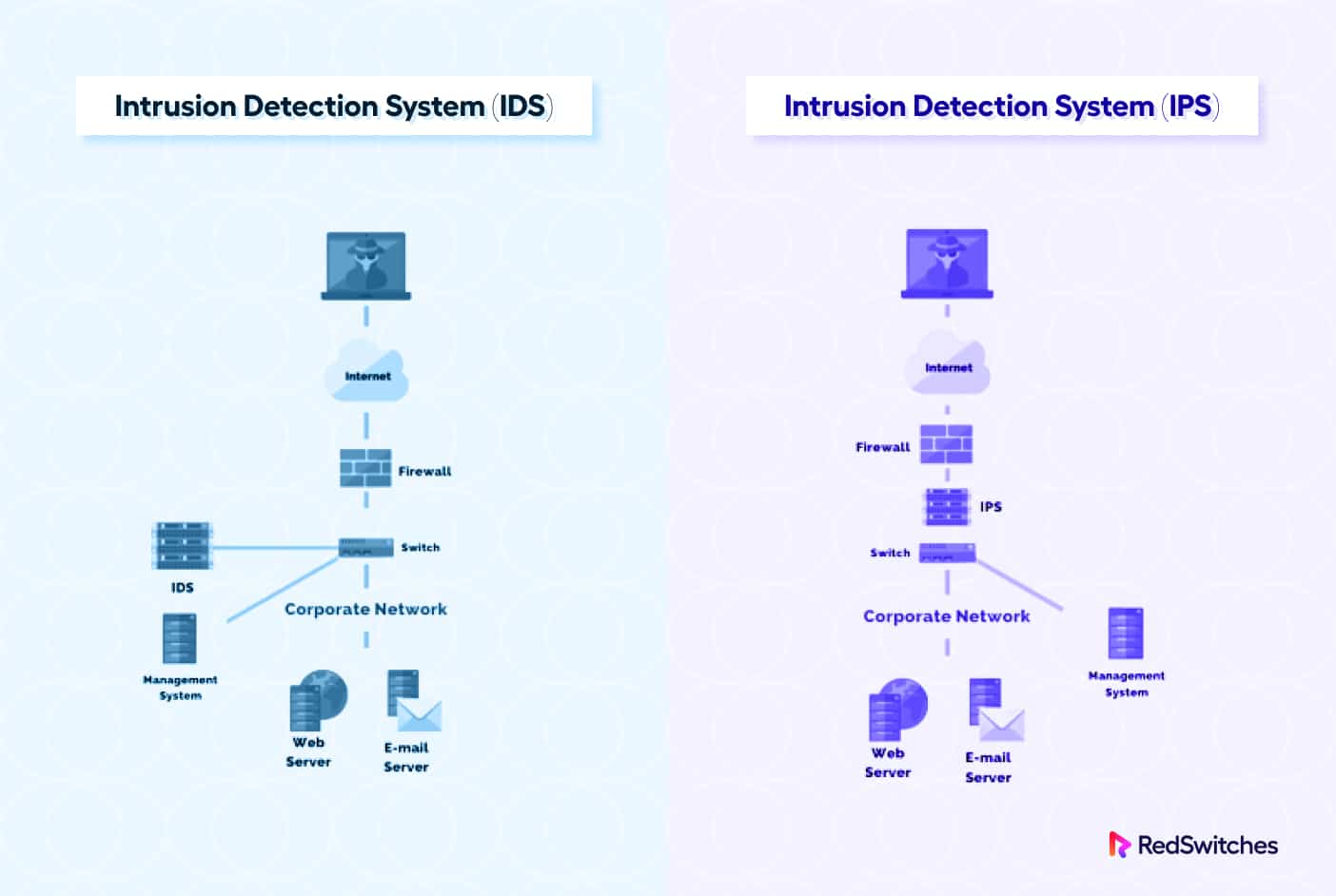
What Is Intrusion Detection and Prevention System? Definition, Examples, Techniques, and Best Practices - Spiceworks